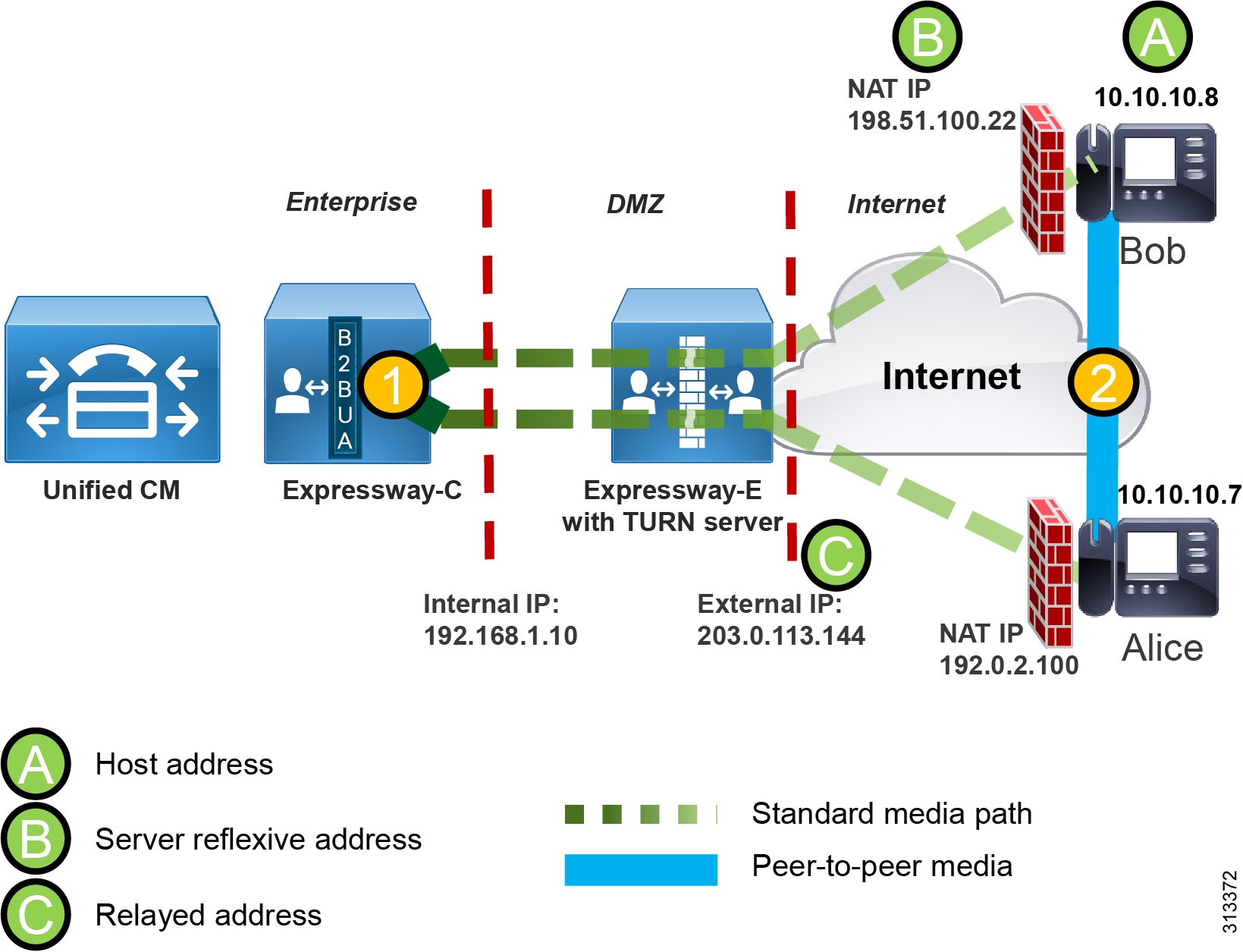
Media Optimization with ICE Enablement in Cisco Enterprise Collaboration Preferred Architecture 12.5 - Cisco
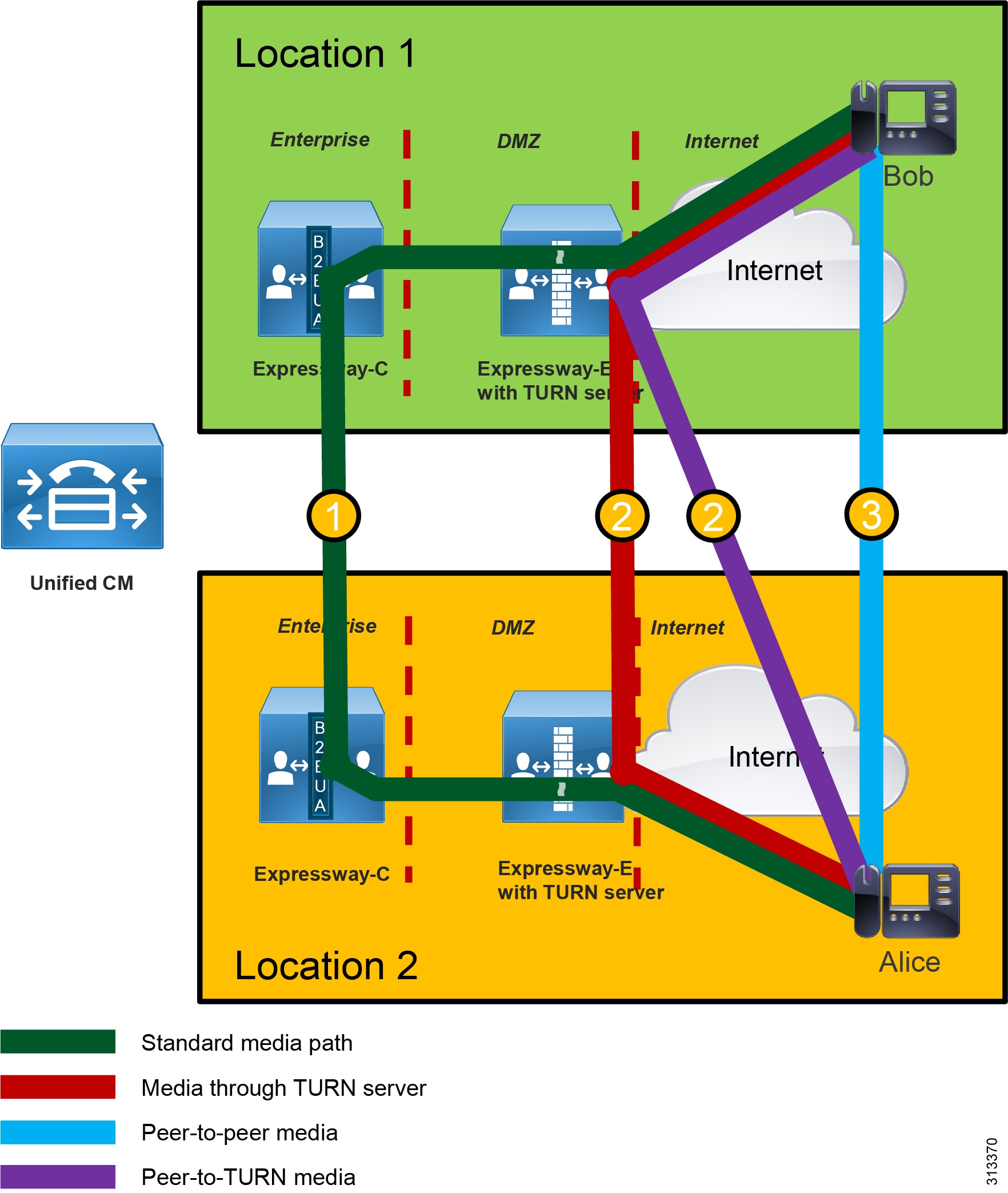
Media Optimization with ICE Enablement in Cisco Enterprise Collaboration Preferred Architecture 12.5 - Cisco
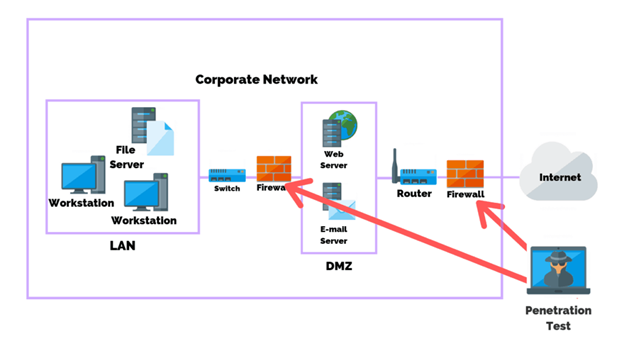
What is WAN, LAN, and DMZ? How does it relate to a firewall setup? I'm learning about firewalls, and I'm confused on this. - Quora

![PDF] NVP: A Network Virtualization Proxy for Software Defined Networking | Semantic Scholar PDF] NVP: A Network Virtualization Proxy for Software Defined Networking | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/0b3ae1bbfd084226c93ef4b48cf2dc7982a61998/7-Figure2-1.png)







/cdn.vox-cdn.com/uploads/chorus_asset/file/13996416/2012_mpls_bypass.1419970333.png)
